Topics: Security Information, Event Management
Introduction
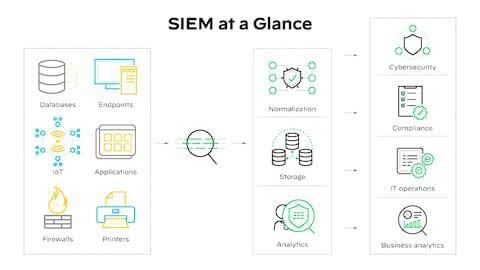
It is always wise to be prepared for any kind of threat. Be it a medical emergency or national security issues, the present times require us to be ready for any future threats to protect us from heavy losses. Similarly, one essential component of cybersecurity is – security information and event management (SIEM) solution. SIEM includes collection, aggregation and analysation of large volumes of data from organization-wide applications, devices, servers and users in real time. All this data is consolidated in a single, unified platform to provide a comprehensive view on organizations or institutes security posture, security operations center (SOC) to detect, investigate, and respond to security incidents effectively.
SIEM technology was introduced in 2005 by Gartner. And ever since it evolved into a critical tool for threat detection, investigation and response (TDIR). Combining security information management (SIM) and security event management (SEM), SIEM now supports comprehensive cybersecurity management, control and compliance. Some key aspects of SIEM are as follows –
1. Data Aggregation –
SIEM consolidates and collects log data and event information from device sources like servers, applications, network devices and security tools.
2. Threat Detection –
SIEM can be used to analyse User and Entity Behaviour Analytics (UEBA), the technology can identify suspicious activities related to malware and other potential security breaches.
3. Correlation and Analysis –
SIEM has been gaining popularity because of its ability to carefully analyze and provide implications and future outputs on the basis of the current information that has been fed to it. This not only provides organizations with reliable future prospects but also helps in tackling cyber threats.
5. Data Storage –
SIEM technology aids greatly in consolidating complex and large data safely and for security analysis and incident response.
5. Real-Time Monitoring –
SIEM helps in early detection of threats and provides reliable and effective measures to tackle security issues and other organization related management.
6. Historical Analysis –
Historical analysis helps in understanding the past aspects of security information and event management which further helps in understanding the future applications and implications about the same effectively and efficiently.
7. Phishing Detection –
SIEM solutions can analyse email traffic, and flag phishing attempts. SIEM can identify mass phishing emails sent to employees in the organizations with malicious links.

Another Important Aspect of SIEM is – How and Where Can it be Applied?
- Threat Detection and Responses – Detecting a wide range of attacks including malware, ransomware, brute-force attacks and Distributed Denial of Services (DDoS)
- Cloud Security Monitoring- Detection of misconfigurations or unauthorized access within cloud platforms and SaaS applications.
- Advanced Persistent Threat (APT) Detection – This method correlates benign events over a long period of time and provides reliable data about the future implications.
- IoT Security – This system monitors the behavior of connected internet of things devices to highlight deviations from expected authority.
- Compliance Management – Generates automated reports and provides audit trials to highlight adherence to regulations, which is important in industries like financial services, healthcare, and government.
Some Key Advantages of Implementing SIEM Solutions are as Follows
- Increased security effectiveness and faster response to threats.
- Efficient compliance demonstrations.
- Significant reduction in complexity.
SIEM Can be Used Effectively is Certain Practices are Taken Up by Organizations Such as –
- Outline Clear Objectives – Use specific security applications and add more eventually. Slow and gradual use of security applications leads to faster familiarization with the system and can be used efficiently.
- Train the Team – The application of SIEM can be successful if the employees are trained to get familiarized and eventually use it.
- Regular Updates and Reviewing – It is necessary to understand the lacunas that are faced by the employees and the SIEM system to make it more effective for the future security threat detection.
- Customise Correlation Rules – The SIEM technology needs to be customized according to the use and need of the company, as every organisation has unique needs and cybersecurity risks.
- Integrate Data Sources – Ensure that all key security systems, such as firewalls, endpoints, and other applications, are integrated with SIEM.
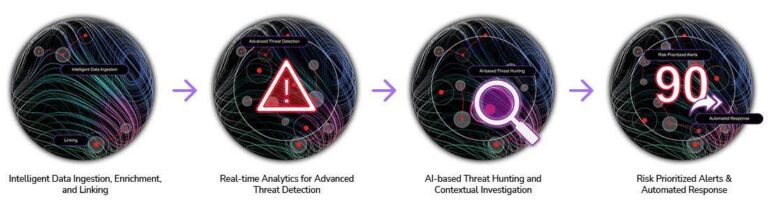
Security is one of the most important investments that brings additional value over time. A good quality SIEM technology depends upon adaptability and is designed to be scalable for growing companies. Utilization of AI is promising in improving processes and new threats. One of the main reasons for companies to adopt SIEM is because it helps them avoid the costs associated with security breaches. SIEM technology is programmed to continually take in and process data, hence the investment pays off. As technology grows SIEM solutions grow with it and helps in providing security threat detections along different timelines and needs.
Conclusion
SIEM is thus a foundational and indispensable technology in a modern cybersecurity strategy, shifting organizations from a reactive to a proactive security posture provided it is properly implemented, tuned, and managed in alignment with specific business needs and goals.
References
[1] “What are SIEM use causes,” Paloalto. [Online].
Available: https://share.google/IkXqu1gStbZx2XoXz
[2] “What is SIEM?How security information and event management works,”.Fortinet. [Online].
Available: https://share.google/CKlfidzLZ7e9Cj1Xl
[3] “SEIM implementations guide|How to get started with SEIM tools,”BitLyft Cybersecurity. [Online].
Available: https://share.google/MS78pmNI0tb69VfuE
[4] What is SEIM in cybersecurity?,”.Gurucul. [Online].
Available: https://share.google/UL91uDTfv8NVlFOKG
[5] “10 benefits you need to know”,.SentinelOne.[Online].
Available:https://share.google/fujGDHudLlba5ryUf
FAQs
Q1. What is SIEM in cybersecurity?
SIEM combines Security Information from logs and events into one platform for real-time threat detection and centralized monitoring.
Q2. Why is SIEM Event Management important?
Event Management in SIEM helps detect, correlate, and prioritize security incidents so teams can respond faster and smarter.
Q3. How does SIEM collect security information?
SIEM gathers Security Information from servers, networks, cloud apps, and endpoints, unifying them for analysis.
Q4. What types of events does SIEM manage?
SIEM handles cyber events like phishing, malware, login anomalies, and network alerts using structured Event Management.
Q5. Can SIEM detect phishing events?
Yes, SIEM analyzes email activity as part of Event Management and flags phishing threats using live Security Information signals.
Q6. How does SIEM support Zero Trust security?
SIEM feeds verified Security Information into continuous monitoring systems, aligning with strict access validation models.
Q7. What challenges exist in SIEM event management?
Complex data sources, tuning rules, and user training are common hurdles when scaling Event Management in SIEM.
Q8. How often should SIEM rules be updated?
SIEM correlation rules should be updated regularly to keep Security Information insights accurate and threat-ready.
Q9. Who manages SIEM event management systems?
SOC analysts, IT security teams, and trained campus or enterprise staff handle Event Management workflows.
Q10. What is the future of SIEM?
Future SIEM will use AI to enhance Event Management, anomaly detection, and smarter identity-based Security Information analysis.
Penned by Krushna
Edited by Pranjali, Research Analyst
For any feedback mail us at [email protected]
Transform Your Brand's Engagement with India's Youth
Drive massive brand engagement with 10 million+ college students across 3,000+ premier institutions, both online and offline. EvePaper is India’s leading youth marketing consultancy, connecting brands with the next generation of consumers through innovative, engagement-driven campaigns. Know More.
Mail us at [email protected]