Identity and Access Management (IAM): Concepts, Applications, Challenges and Future Directions Ahead
Topics: Access Control, Zero Trust
Introduction
In an era marked by rapid digital transformation, organizations increasingly rely on cloud services, remote work models, and interconnected digital ecosystems. While these developments have enhanced efficiency and accessibility, they have also significantly expanded the attack surface for cyber threats. Unauthorized access, data breaches, identity theft, and insider threats have become recurring challenges across both public and private sectors. In this context, Identity and Access Management (IAM) has emerged as a foundational pillar of modern cybersecurity. IAM systems are designed to ensure that the right individuals have the right access to the right resources at the right time, and for the right reasons. As digital identities become central to governance, commerce, and national security, IAM plays a critical role in safeguarding trust, data integrity, and operational resilience.
Definition of Identity and Access Management (IAM)
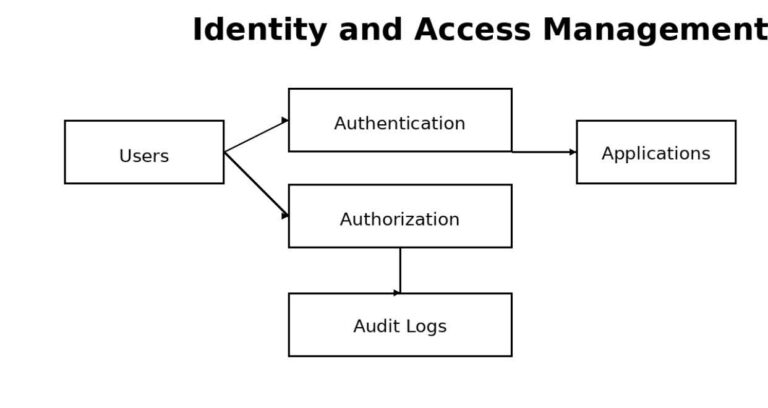
Identity and Access Management refers to a framework of policies, processes, and technologies that enables organizations to manage digital identities and regulate user access to information systems. IAM ensures that users—whether employees, customers, partners, or devices—are properly authenticated and authorized before gaining access to resources. It involves identity creation, authentication, authorization, role assignment, access monitoring, and lifecycle management. In simpler terms, IAM answers three fundamental questions: Who are you? What are you allowed to access? And under what conditions? By centralizing identity controls, IAM helps organizations maintain security while enabling seamless user experiences.
Uses of IAM –
IAM systems are used across a wide range of sectors including government, banking, healthcare, education, and technology.
- One of the primary uses of IAM is secure user authentication –
often through mechanisms such as multi-factor authentication (MFA), single sign-on (SSO), and biometric verification. These tools reduce reliance on passwords and minimize the risk of credential-based attacks. - IAM is access control management. IAM ensures that users can access only those systems and data necessary for their roles, following the principle of least privilege. This is particularly crucial in large organizations with complex hierarchies and sensitive data.
- IAM is also widely used in regulatory compliance and auditing. By maintaining logs of user access and activity, IAM helps organizations comply with data protection laws, cybersecurity regulations, and governance standards.
- IAM supports remote and cloud-based work environments – allowing secure access across devices and locations without compromising security.
Advantages of IAM –
- One of the most significant advantages of IAM is enhanced security – By reducing unauthorized access and limiting privileges, IAM lowers the risk of data breaches and cyberattacks. Advanced IAM solutions can also detect suspicious behavior and respond in real time.
- IAM also Improves Operational Efficiency – Automated user provisioning and de-provisioning reduce administrative burdens and minimize human error. Employees gain faster access to required systems, improving productivity and user satisfaction.
- Better Governance and Compliance – IAM provides visibility into who has access to what, enabling organizations to enforce policies consistently and demonstrate accountability during audits.
From a strategic perspective, IAM enhances digital trust. Customers and users are more likely to engage with platforms that protect their identities and personal data, making IAM a key enabler of digital transformation and innovation.
Problems Faced in IAM Implementation –
Despite its benefits, IAM implementation is not without challenges.
- One major problem is complexity.
- IAM across legacy systems, cloud platforms, and third-party applications can be technically demanding and resource-intensive.
- User Resistance and Usability Issues – Overly complex authentication processes may frustrate users and lead to poor adoption or risky workarounds. Balancing security with user convenience remains a persistent concern.
- Cost and Scalability – Also pose difficulties, particularly for small and medium organizations. Advanced IAM solutions may require significant investment in infrastructure, skilled personnel, and continuous updates.
- IAM Systems Themselves Can Become Targets if Not Properly Configured – Misconfigurations, inadequate policy definitions, and poor identity governance can undermine the effectiveness of IAM and create new vulnerabilities rather than eliminating existing ones.
Way Forward –
The future of IAM lies in adopting intelligent, adaptive, and user-centric approaches. One key direction is the shift towards Zero Trust Architecture, where no user or device is trusted by default, even within the organizational network. Continuous verification becomes central to access decisions. The integration of artificial intelligence and machine learning can further strengthen IAM by enabling behavioral analytics, anomaly detection, and predictive risk assessment. These technologies allow IAM systems to respond dynamically to evolving threats.
Organizations must also invest in identity governance and policy clarity, ensuring that access rights are regularly reviewed and aligned with organizational roles. Capacity building, training, and awareness are equally important to ensure effective IAM adoption. At a broader level, governments and institutions should promote standardization and interoperability in IAM frameworks, especially as digital public infrastructure expands. Strong legal and regulatory backing can further enhance accountability and trust.
Conclusion
Identity and Access Management has become indispensable in an increasingly digital and interconnected world. As identities form the backbone of digital interactions, securing them is no longer optional but essential. IAM not only protects systems and data from unauthorized access but also enables organizations to operate efficiently, comply with regulations, and foster trust among users. While challenges related to complexity, cost, and usability persist, continuous innovation and strategic implementation can address these issues effectively. Moving forward, a robust and adaptive IAM framework will be critical in ensuring secure, inclusive, and resilient digital ecosystems. In essence, IAM is not just a cybersecurity tool it is a cornerstone of modern digital governance and trust
References–
[1] “What is identity access management ( IAM),”. Microsoft Security.[Online].
Available:https://www.microsoft.com/en-in/security/business/security-101/what-is-identity-access-management-iam
[2] “What is identity and access management(IAM)? A guide to IAM,”Sailpoint.[Online].
Available:https://www.sailpoint.com/en-au/identity-library/identity-and-access-management?igaag=159214277179&igaat=&igacm=20902576498&igacr=691326915089&igakw=enterprise%20identity%20security&igamt=p&igant=g&campaignid=20902576498&utm_source=google&utm_network=g&utm_medium=cpc&utm_content=apac-in-isc&utm_term=enterprise%20identity%20security&utm_id=7012J000001Fba9&gad_source=1&gad_campaignid=20902576498&gbraid=0AAAAADyJpazmShE1D_gNKRBtN8Ef4VZqH&gclid=Cj0KCQiAr5nKBhCpARIsACa_NiNKWTQ0enEOWSJ6Pj_-k_NBnLPPel0rtPGfrqRpT5BCqMcz1E44sY8aAuytEALw_wcB
[3] “ Identity fundamentals – Identify and Access management,”.PingIdentity.[Online].
Available:https://share.google/7hZOR6SqEBmSDGNc1
[4] “IBM verify:secure, frictionless access for every identity,”.IBM.[Online].
Available:https://www.ibm.com/products/verify?utm_content=SRCWW&p1=Search&p4=93820598&p5=e&p9=171090011486&gclsrc=aw.ds&gad_source=1&gad_campaignid=22049586208&gclid=Cj0KCQiAr5nKBhCpARIsACa_NiN8ipJr6uoRPTG06l7Twfsvfm-IH4cxTqKUicFld9ph-vtV3OdXTMMaAv-pEALw_wcB
FAQs
Q1. What is IAM Access Control?
Access Control in IAM ensures only verified users get role-based access, reducing unauthorized entry and protecting sensitive systems.
Q2. How does Zero Trust enhance IAM security?
Zero Trust strengthens IAM by verifying every identity continuously, ensuring no user or device is trusted by default.
Q3. Why is Access Control important for cloud platforms?
Cloud platforms increase security risks. Strong Access Control limits privileges and prevents unauthorized data exposure.
Q4. What is Zero Trust authentication?
Zero Trust authentication validates users at every step using signals like behavior, device, and access patterns.
Q5. Can Access Control reduce insider threats?
Yes. IAM-based Access Control ensures least privilege access, lowering the risk of internal misuse.
Q6. Is Zero Trust useful for remote work security?
Absolutely. Zero Trust ensures secure access across locations, protecting systems beyond office networks.
Q7. What are the principles of Access Control in IAM?
Core principles include least privilege, role-based access, and monitored Access Control for every user.
Q8. What challenges does Zero Trust solve in IAM?
Zero Trust helps reduce identity theft, unauthorized access, and internal trust-based vulnerabilities.
Q9. How often should Access Control policies be reviewed?
Policies should be reviewed regularly to keep Access Control updated and aligned with security needs.
Q10. What is the future of Zero Trust in colleges and enterprises?
IAM will increasingly adopt AI-driven identity systems and Zero Trust frameworks for safer digital ecosystems.
Penned by Krushna
Edited by Pranjali, Research Analyst
For any feedback mail us at [email protected]
Transform Your Brand's Engagement with India's Youth
Drive massive brand engagement with 10 million+ college students across 3,000+ premier institutions, both online and offline. EvePaper is India’s leading youth marketing consultancy, connecting brands with the next generation of consumers through innovative, engagement-driven campaigns. Know More.
Mail us at [email protected]